Learn to identify hacker attacks targeting your infrastructure in Solarpunk. Recognize the signs and respond swiftly to mitigate digital threats.
The ability to swiftly and accurately identify a hacker attack is the first and most critical step in mitigating its impact. In Solarpunk™, digital intrusions can manifest in subtle ways, often disguised as system glitches or network slowdowns, making early detection a significant challenge. Recognizing the tell-tale ss of a cyber intrusion is paramount to preventing widespread damage, data breaches, or the disruption of essential services like your solar energy grid or automated farming systems. A delayed or missed identification can allow attackers to deepen their foothold, exfiltrate valuable information, or even seize control of vital infrastructure, leading to catastrophic consequences for your eco-city. Vigilance and a keen understanding of normal system behavior are your primary defenses.
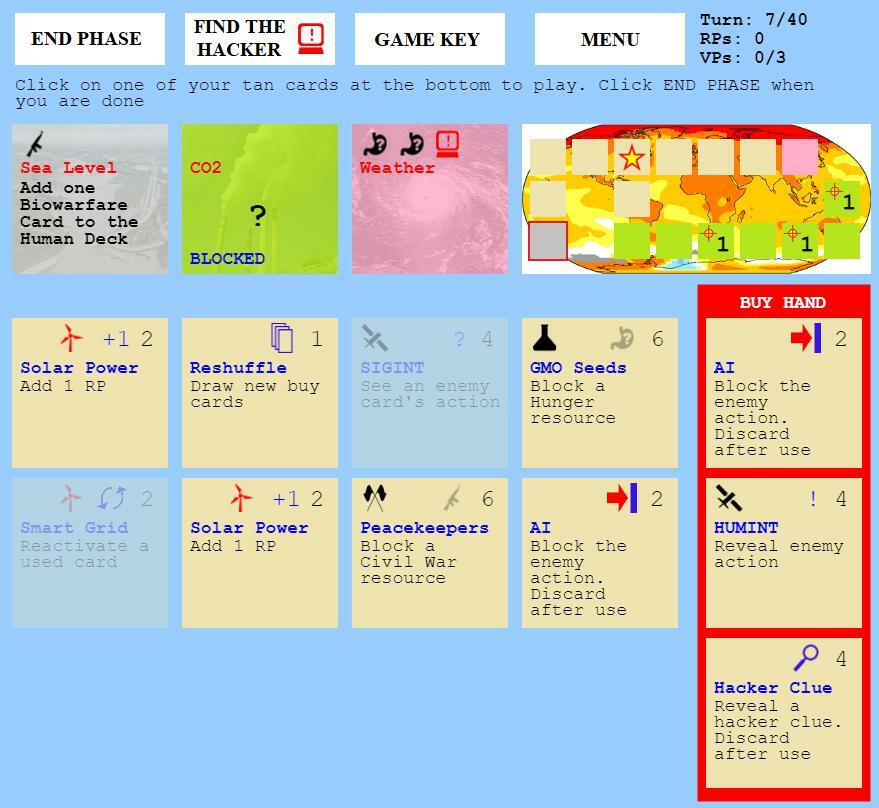
The game provides several indicators that can signal a potential cyberattack. These range from unusual network traffic patterns and unexpected system resource spikes to unauthorized access attempts and the sudden unavailability of critical services. Monitoring your network logs, system performance metrics, and security alerts is an ongoing process that requires dedicated attention. Furthermore, anomalies in data integrity, such as corrupted files or unexpected data modifications, can also point towards malicious activity. It is crucial to establish baseline performance metrics for your systems so that deviations are immediately noticeable. By understanding these indicators and maintaining a constant state of awareness, You can significantly improve their chances of detecting and responding to hacker threats before they escalate into full-blown crises. This proactive approach to identification is the bedrock of a secure and resilient digital infrastructure in Solarpunk™.
Key Indicators of a Cyberattack
- Unusual Network Traffic: Sudden spikes in outbound or inbound network traffic, especially to unknown or suspicious IP addresses, can indicate data exfiltration or command-and-control communication.
- System Performance Degradation: Unexpected slowdowns, unresponsiveness, or frequent crashes of servers, workstations, or critical systems like the Hydroponic Control Unit can be a s of resource exhaustion due to malicious processes.
- Unauthorized Access Attempts: Repeated failed login attempts, unusual login times, or access from unexpected geographical locations can signal brute-force attacks or credential stuffing.
- Suspicious Process Activity: The appearance of unknown or unauthorized processes running on your systems, especially those consuming high CPU or memory resources, warrants immediate investigation.
- Data Integrity Anomalies: Corrupted files, unexpected data modifications, or the sudden disappearance of data can be indicators of ransomware attacks or deliberate data destruction.
- Alerts from Security Software: Pay close attention to alerts generated by your intrusion detection systems, antivirus software, or other cybersecurity tools. These are often the first line of defense in flagging suspicious activity.
- Disruption of Services: The sudden and unexplained unavailability of critical services, such as the power grid management system or the communication network, is a strong indicator of a targeted attack.
Establishing a Monitoring Framework
- Centralized Logging: Implement a centralized logging system to collect and analyze logs from all your network devices and servers, making it easier to correlate events and identify patterns.
- Real-time Monitoring Tools: Utilize network monitoring tools that provide real-time visibility into network traffic, system performance, and security events.
- Behavioral Analysis: Employ security solutions that use behavioral analysis to detect anomalies in user and system behavior, which can often indicate a compromise.
- Regular Log Review: Schedule regular reviews of system and security logs, even when no immediate alerts are present, to catch subtle ss of intrusion.
- Alert Prioritization: Develop a system for prioritizing security alerts based on their potential impact, ensuring that the most critical threats are addressed first.
100% Human-Written. AI Fact-Checked. Community Verified. Learn how AntMag verifies content