Learn how to complete the 'Extract Intel' objective in Intravenous 2: Mercenarism with this detailed walkthrough. Get tips and strategies to succeed.
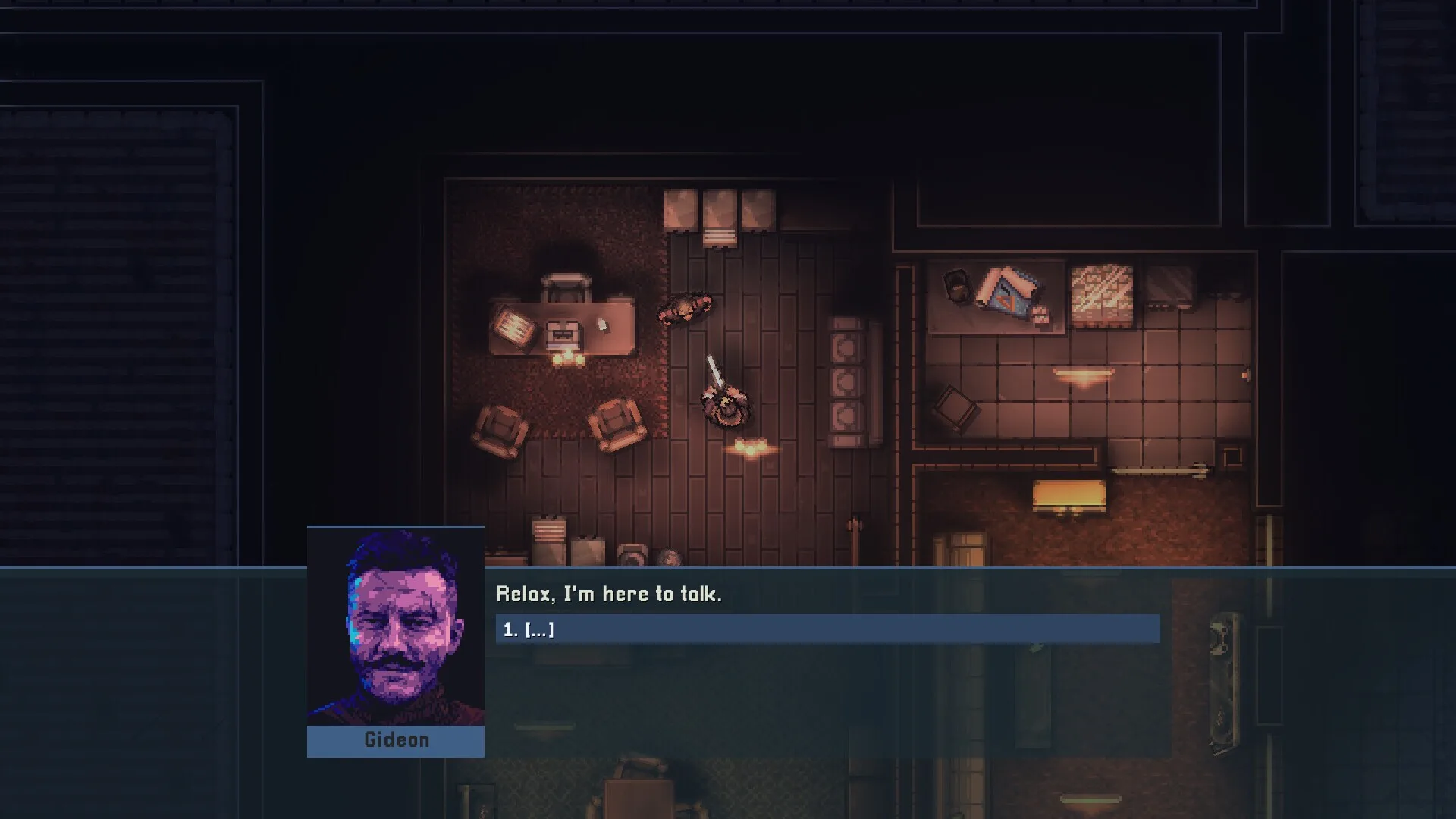
This section of the guide is dedicated to helping you tackle the 'Extract Intel' objective in Intravenous 2: Mercenarism. We'll break down the steps to ensure you can grab that intel without too much trouble.
Walkthrough
- 1Objective Start: You'll begin the mission with the primary goal of acquiring specific intelligence. Keep an eye on your objective marker for the general direction.
- 2Infiltration: Approach the target location stealthily. Look for entry points that offer the best cover or the least resistance. This might involve using vents, disabling cameras, or taking out guards quietly.
- 3Locate the Intel: Once inside the facility or area, you'll need to find the exact location of the intel. This could be on a computer, a physical document, or held by a specific NPC. Use your map and any available intel (like overheard conversations or documents found earlier) to pinpoint its exact location.
- 4Acquire the Intel: Interact with the intel source. This might be a simple button press to download data, or it could involve a mini-game or a more complex interaction depending on the game's mechanics. Be prepared for potential alarms if you're detected.
- 5Exfiltration: With the intel secured, your next step is to get out. Retrace your steps or find a new, safer exit route. Be aware that security might be heightened after you've acquired the intel, so be ready for increased enemy presence or new security measures.
Tips
- Always prioritize stealth. If you can avoid combat, do so. It conserves ammo and reduces the chance of raising alarms.
- Utilize your gadgets. Items like silenced weapons, EMP grenades, or hacking tools can be invaluable for bypassing security and neutralizing threats without direct confrontation.
- Listen to your surroundings. Audio cues can alert you to enemy patrols or nearby security systems.
- If the intel is on a computer, check if you can remotely access it or disable nearby security systems before making your move.
- Have a backup exfiltration plan. Sometimes your entry point might become compromised, so knowing an alternative way out is crucial.
100% Human-Written. AI Fact-Checked. Community Verified. Learn how AntMag verifies content